The 411 on Credential Stuffing
Credential stuffing is easily the most common technique of account takeover AND the primary use of breached usernames and passwords. With billions of stolen credentials for sale on the dark web, the automation of credential stuffing has become a hot (and efficient) business for fraudsters. Here is what you need to know to keep yourself safe.
What is it
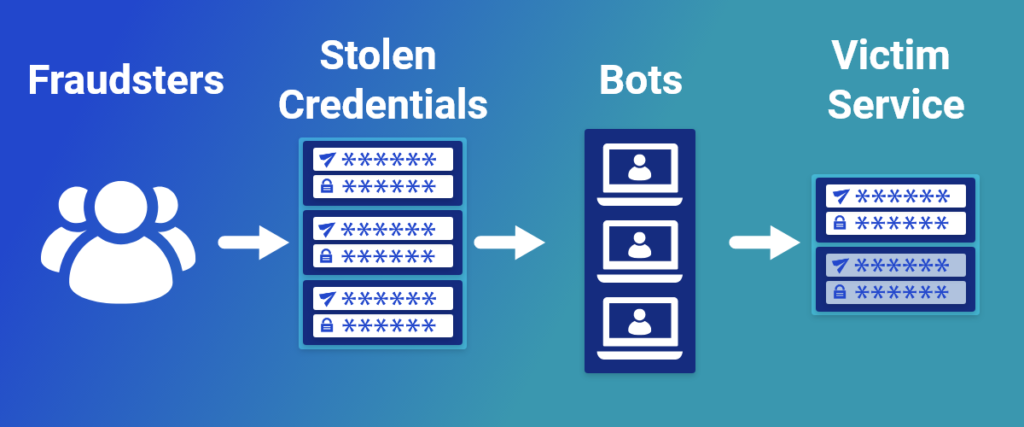
Credential stuffing is a type of cyberattack where a large set of account usernames (or emails) and passwords are used to gain access to accounts on a website. These credentials are often from data breaches. The attack is done with automated login attempts making it both cheap and efficient for fraudsters, unlike other “brute force” attacks where fraudsters attempt to guess a user’s password.
With a collection of a million credentials, the fraudster only needs about 1,000 of those to work for it to be profitable on one website (often from access to credit card numbers or sensitive data). They can repeat this process as many times as they like on site after site.
How does it work
“How does it work so well?” may be the more appropriate question to ask. Fraudsters have access to billions of credentials. Many of those credentials contain passwords that were not changed after the original breach occurred. Around 64% of passwords are still being used AFTER being exposed in a data breach and 82% of those passwords are an exact match! Even if you’ve changed your password for the site that was breached, if you’re still using it across other accounts online you are at risk.
With this high rate of username and password reuse, fraudsters can submit those credentials to hundreds of other sites easily. Those accounts can then be compromised.
Now, you may be thinking “what does it really matter if someone breached my old Dropbox account in 2012?” Well, this breach resulted in 68 million sets of credentials being sold on the dark web in 2016. Consider who is involved in those 68 million emails and passwords. In spite of Dropbox’s best efforts, it is unlikely that those people all updated their passwords. What if one of them is a high-level government official, CEO, or your boss? What if they use that same password to log in to approve your payroll?
These credentials fuel the underground economy and are used for everything from spam to phishing and account takeovers.
What you can do
For such a common and serious attack, it’s actually quite simple to decrease your risk. Credential abuse is involved in 89% of website breaches, so today is the day to level up your password hygiene.
- Stop reusing passwords across different sites.
- Regularly change your passwords.
- Use a password manager to manage, create, and store your unique passwords.
Sources:
https://spycloud.com/resource/2022-annual-identity-exposure-report/
https://www.cloudflare.com/learning/bots/what-is-credential-stuffing/
https://www.wired.com/story/what-is-credential-stuffing/